Without a cyber security policy, your organisation is vulnerable. Criminals can exploit weaknesses in your systems or gaps in your employees’ knowledge to steal data, disrupt operations or hold your business to ransom. Damage worsens when staff don’t know how to handle or report these cyber-attacks.
Our guide explains how to create a cyber security policy to educate staff and protect your organisation. It covers what to include and why small and medium businesses must prioritise digital safety.
Cyber security is protecting computer systems and networks from attacks. Methods range from straightforward (password management, for example) to complex digital safeguards, working behind the scenes. This variety is necessary because of the complexity of modern digital systems and the scope of cyber-attacks.
The most important protection is staff awareness. People are typically the most significant vulnerability in any system – using weak passwords, clicking questionable links and failing to install security updates are all common oversights. Developing a cyber security policy raises awareness of these pitfalls and helps staff recognise where they might go wrong.
Every organisation, particularly small to medium-sized businesses, is a potential target of a cyber-attack because of a perceived digital weakness. Criminals assume that smaller enterprises lack the knowledge or resources to protect against sophisticated cyber threats. And often, they’re right.
According to government research, some 32% of all surveyed businesses suffered some form of cyber-attack in 2022. Hackers also went after non-profits, with 24% of charities reporting the same.
Interestingly, while 32% of businesses overall recalled an attack, filtering the data by organisation size suggests larger firms should be more concerned. A massive 69% of large companies dealt with a cyber-attack over the same period, losing an average of £4,960 in the process (compared to the overall average loss of £1,100).
But these figures are all relative. Larger organisations with higher turnovers are more prominent targets. When an attack is successful, it’s more expensive to fix because of its complex systems. Generally, big firms can absorb these losses, while smaller firms can’t. So, although owners of small companies might not face cyber threats as consistently, it can be much more devastating when one gets through.
A cyber security policy also helps compliance with the Data Protection Act 2018, which legislates the UK’s General Data Protection Regulation (GDPR). You can read more about GDPR but, in summary, any organisation has a legal duty to protect their customers’ personal data. If you process any information that can be used to identify someone, it must be kept secure and confidential.
Should a data breach happen, you must report it to the International Commissioner’s Office (ICO) as soon as possible or face legal consequences. A formal cyber security policy lets you map out how to handle an attack. Following a plan saves time and confusion should the worst happen, allowing you to meet ICO’s tight timelines and stop problems from escalating.
Start with the context. Employees are more likely to follow a policy if they understand why it exists, so explain why your organisation needs one. Defining roles and responsibilities also helps buy-in, so include this early.
You should also explain the terms and jargon in the policy so everyone can follow it. As with any policy, it must also outline who and what it applies to. Employees, contractors and any other third parties who work with your systems must recognise your policy’s coverage.
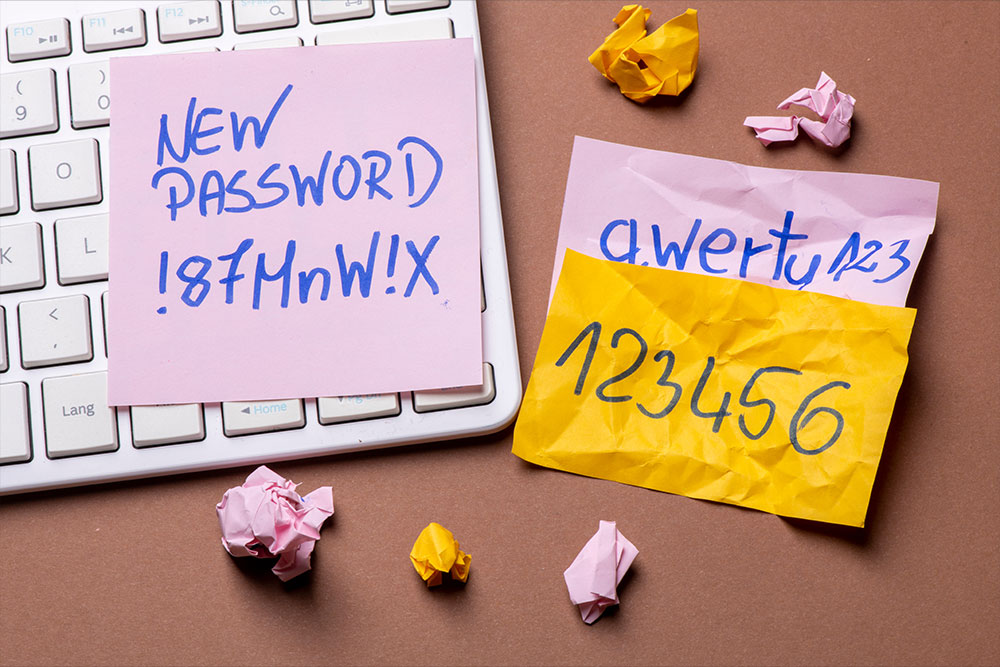
For actual security measures, an excellent place to start is password management. Systems and sensitive information should be password-controlled, but this safeguard only works if employees follow best practices.
Make it clear in your cyber security policy that passwords should be unique (i.e., not using one password for multiple accounts) and challenging to guess. Specifying password requirements – special characters, character length, a mixture of letters and numbers, for example – gives staff ideas on strengthening them. This section should also set out when employees need to change passwords for an added layer of protection against cyber-attacks.
Access control stops unauthorised users from getting to sensitive information or systems. Spell out who can access what and who has the authority to grant or revoke privileges. This safeguard helps keep bad actors out of your systems. It makes it less likely employees will mistakenly access something they shouldn’t.
It’s more helpful for non-scientists to look at how stress affects our thoughts or feelings, which is where the Perceived Stress Scale comes in.
Your emails are a potential vulnerability since they’re mainly handled by real humans. And humans can be fooled into opening malicious links or attachments – a style of attack known as phishing.
Include procedures for dealing with suspicious emails and reporting successful attacks if one gets through.
Criminals will update their strategies, so your software needs to do the same. Software updates keep protections matched to threats and help general performance. Ensure that employees install all updates recommended by the software or system provider. But insist that updates must be official. Hackers can disguise phishing attacks as software patches or updates and emails.
Data backups help keep business continuity should something go wrong. Most of this should be out of your employees’ hands, as automatic backups are generally more reliable and easier to manage. Guidance on data recovery can be helpful, though. We’ve all lost or accidentally deleted important files, which are often entirely retrievable if you know the steps.
Your business has a good chance of being targeted (around one in three, according to the statistics), so you’ve got to plan for a successful attack. And a hack or breach won’t just cost you data. Your reputation could take a hit, and there could be fines or penalties from ICO if they judge you mishandled the incident.
Explain reporting procedures and make it clear who needs to know what. Responsibilities need to be defined, too. Adding more detail to this section will lead to a faster and more efficient response in practice.
Working away from the office can create vulnerabilities. Home or public networks won’t necessarily have the same protections and shared networks are a prominent access point for bad actors. Stress that employees should only ever use trusted, secure networks. You could also advise on general real-world security measures, like keeping devices hidden or locked away when travelling.
Employees need to sign and acknowledge they’ve read and understood the policy, just like any other. Including the consequences of non-compliance might also help motivate staff to follow your guidelines.
And set a policy review date. Like health and safety policies, this should be flexible. Any changes in legislation or actual breaches should trigger an immediate policy review.
Your employees are your biggest weakness in cyber security because most people don’t understand the scale or variety of cyber threats. This lack of awareness often leaves them unable to recognise or respond to such threats. Your cyber security policy should include a section on employee training to overcome this lack of knowledge.
Our online Cyber Security Awareness training course closes knowledge gaps, helping employees spot the different tactics criminals use. The course covers protecting against malware and phishing attacks and promotes general cyber hygiene to prevent common threats.